IP address: knowing and protecting

- Privacy
- Online threats




Overview
An IP address is a unique identifier consisting of numbers and dots used to represent every device on the internet, such as computers, phones, routers, etc. The purpose of an IP address is to allow devices to communicate and exchange data with each other. There are two types of IP addresses : IPv4 and IPv6. IPv4 is currently the most commonly used type, represented by a 32-bit binary number typically separated into four decimal numbers, such as 192.168.1.1. IPv6 was developed as a new type to address the shortage of IPv4 addresses and is represented by a 128-bit binary number typically separated into eight groups of hexadecimal numbers, such as 2001:0db8:85a3:0000:0000:8a2e:0370:7334.
Contents
How can your IP address be obtained?
Is Tracing an IP Address Legal?
What Can People Do with Your IP Address?
How Does MetroVPN Hide Your IP Address?
How can your IP address be obtained?
① Using an IP lookup tool
This is the simplest and most direct method, where you only need to enter a domain name or email address to find the corresponding IP address. There are many free online IP lookup tools, such as whatsmyip.com , whatismyip.live, etc. These tools may also provide some geographic information about the IP address, such as country, city, latitude, and longitude.
② Checking the full header of an email
If you receive an email from a stranger, you can check the full header information of the email. It might contain the sender's IP address. Different email clients have different ways of displaying the email header information, usually found in the email options or details. The email header information may contain multiple IP addresses, and the one closest to the "Received: from" at the beginning is the sender's IP address.
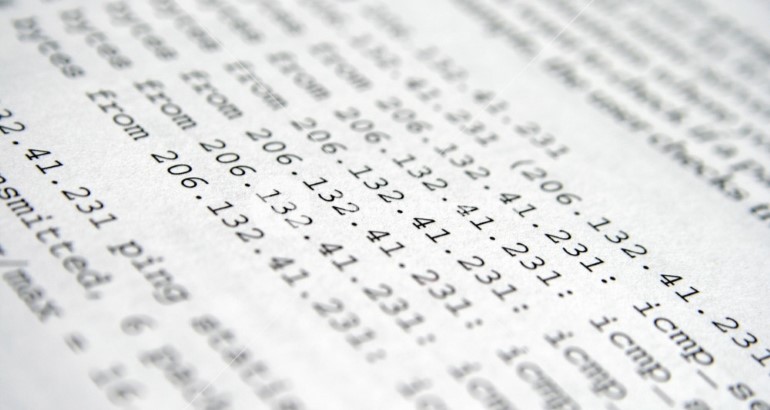
③ Command prompt
If you are using a Windows computer, you can use the command prompt to get the IP address of a domain name or computer device. You only need to open the start menu, search for CMD, and then open the command prompt window. In the DOS interface, enter "ping" and the address you want to trace, then press enter. You will see the target's IP address and response time.
Is Tracing an IP Address Legal?
The legality of tracing an IP address depends on the purpose and method of the tracing. Generally speaking, if tracing an IP address is to solve network issues such as checking network connectivity or troubleshooting, it is legal. However, if tracing an IP address is to violate someone's privacy or perform cyber attacks, it is illegal.
What Can People Do with Your IP Address?
① Track Your Browsing Activity
Your internet service provider manages your network connection and assigns you an IP address. This means that your online activity and devices are visible to your internet service provider. Every time you browse the web, your data is recorded. Besides your internet service provider, some websites, apps, and third-party advertisers can track your browsing history, preferences, interests, and behavior through your IP address to provide customized content and ads.
② Restrict Your Website Access
Some websites decide whether to allow users to access them based on their IP addresses. This may be due to copyright, legal, or other reasons. For example, some video streaming services restrict users from watching certain programs or movies based on their geographic location. Additionally, some website administrators use IP addresses to ban rule-breaking or unwelcome users.
③ Perform Denial-of-Service (DoS) Attacks
A denial-of-service attack (DoS) is a type of network attack that aims to make a target server or device unable to function properly, thus affecting its ability to provide services. Attackers can implement DoS attacks by sending a large number of requests or data packets to the target IP address, causing it to overload or crash.
④ Scan Open Ports
Ports are channels on network devices used to receive and send data. Each port has a number to distinguish different types of data and services. For example, port 80 is usually used for HTTP protocol, and port 443 is used for HTTPS protocol. Attackers can use some tools to scan for open ports on a target IP address to find potential vulnerabilities or intrusion points.
⑤ Conduct Doxing Attacks
Doxing is a form of online harassment that involves threatening, embarrassing, or intimidating individuals by collecting and publicly releasing their personal information. Attackers can use some websites or services to query information related to a target IP address, such as name, phone number, email address, social media accounts, and so on.
⑥ Steal Your Personal Information
Through Vishing Attacks Vishing is a type of phone scam that involves obtaining sensitive information such as credit card numbers, bank accounts, passwords, etc. by impersonating legitimate organizations or individuals. Attackers can use some technical means to spoof their phone number to match the target IP address, thereby increasing credibility.
⑦ Personalize Ads through IP Geolocation
IP geolocation is a technique that uses a user's IP address to determine their geographic location. Some advertisers use this technology to provide users with ads related to their location, such as restaurants, hotels, tourism, etc.
How to Hide Your IP Address?
If you don't want others to know your IP address, you can take some measures to conceal it. This way, you can protect your network privacy and security, and avoid being tracked or attacked. Here are some ways to hide your IP address:
① Use VPN
A VPN is a virtual private network that can connect you to a remote server through an encrypted tunnel, thereby changing your IP address. When you use a VPN, your network traffic is encrypted and scrambled, making it impossible for outsiders to see your real IP address and network activity.
② Use Proxy Server
A proxy server is an intermediate server that can pass data between you and the target website. When you use a proxy server, your request is sent to the proxy server first, then forwarded to the target website by the proxy server. This way, the target website sees the proxy server's IP address instead of yours.
③ Use Tor Browser
The Tor browser can allow you to access the internet through a distributed anonymous network. When you use Tor browser, your network traffic is divided into multiple layers of encrypted data packets, which are transmitted through multiple randomly selected relay nodes. This way, each node can only see the previous and next node's IP addresses, but not your real IP address or the target website. The Tor browser can provide high anonymity and privacy protection, but also has some drawbacks, such as slow speed and limited functionality.
How Does MetroVPN Hide Your IP Address?
If you want to hide your IP address, using a VPN is a good choice. A VPN is a virtual private network that can connect you to a remote server through an encrypted tunnel, thereby changing your IP address and location. This way, you can avoid being tracked and monitored, while also accessing some blocked or restricted websites and content.
However, not all VPNs are the same. Some VPNs may log your activity, some VPNs may lower your internet speed, and some VPNs may leak your real IP address. Therefore, you need to choose a reliable, fast, and secure VPN to protect your network privacy and security.
MetroVPN is an excellent VPN service provider with the following features:
① Easy to use
You don't need to register or log in, just one-click connection, and you can enjoy MetroVPN 's service.
② Hide IP Address
MetroVPN has 6500+ stable VPN servers covering multiple countries and regions worldwide. You can switch servers anytime to change your IP address and location.
③ Strict no-logs
MetroVPN does not record or store your browsing history, traffic data, or personal information. Your network activity is known only by yourself.
④ Ultra-high speed
MetroVPN uses advanced technology to ensure a high-speed and stable connection, allowing you to seamlessly watch videos, play games, download files, and more.
⑤ Access Restricted Content
MetroVPN can help you access some blocked or restricted websites and content, such as Netflix, Hulu, BBC iPlayer, and more.
⑥ Risk Barrier
MetroVPN can help you block some annoying ads, trackers, and malware, improving your network experience and security.
In summary, by using MetroVPN , you can hide your IP address and protect your network privacy and security effectively.






